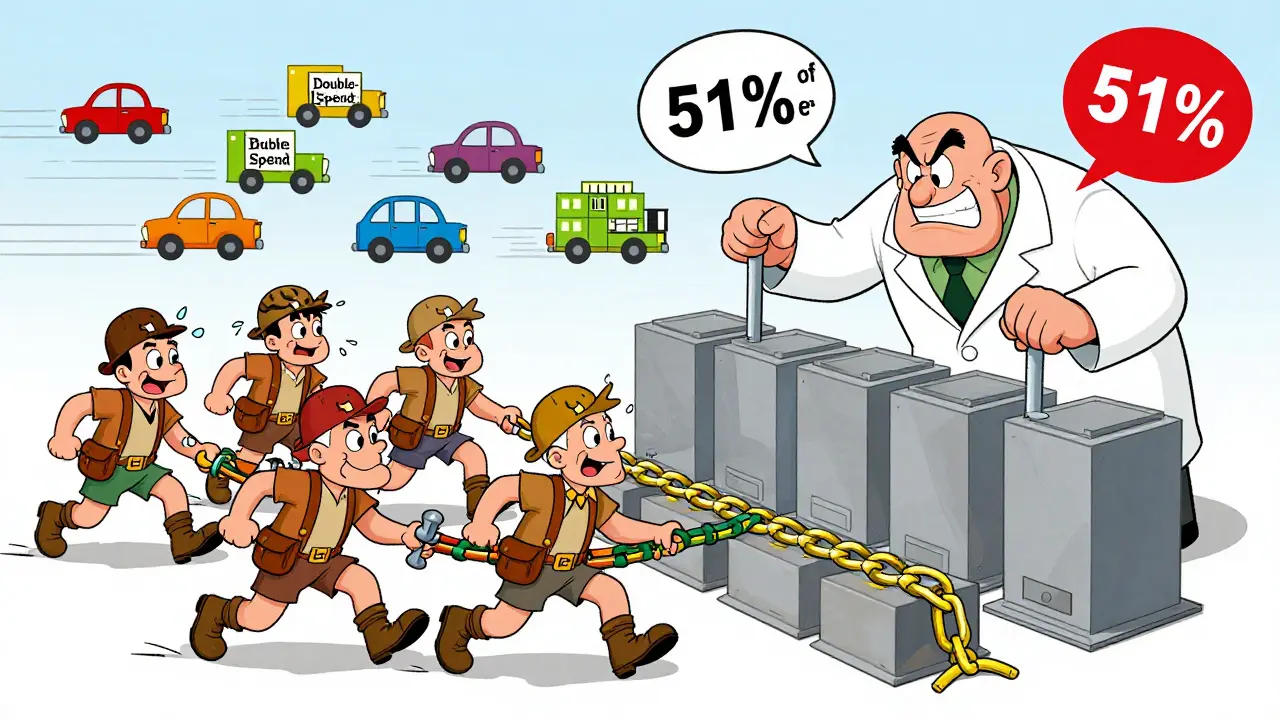
A 51% attack sounds like science fiction, but it’s a real threat that’s happened more than once-and it could happen again. At its core, it’s when one person or group takes control of more than half of a blockchain’s mining power. That’s it. No magic. No hacking into wallets. Just raw computing power. And when they have that much control, they can break the rules of the network-without breaking the code.
How a 51% Attack Actually Works
Blockchains like Bitcoin and Ethereum Classic use something called Proof of Work (PoW). Miners compete to solve math puzzles. The first one to solve it gets to add the next block of transactions and earns a reward. The network trusts the longest chain because it’s assumed to represent the most work done. Here’s the twist: if someone controls over 50% of all the mining power on a network, they can outpace everyone else. They don’t need to crack encryption or steal private keys. They just need to build a longer chain faster than the rest of the network can. Imagine you’re playing a game where everyone writes down transactions on paper. The rule is: the version with the most pages wins. Now imagine you secretly have 51% of all the paper in the room. You can write your own version faster than anyone else. You can erase someone else’s transaction and replace it with one that sends the same money to you instead. That’s double-spending. And it’s exactly what a 51% attack enables.What an Attacker Can-and Can’t-Do
Let’s be clear: a 51% attacker doesn’t have superpowers. They can’t:- Steal coins from other people’s wallets
- Create new coins out of thin air
- Change the rules of the blockchain (like altering the 21 million Bitcoin limit)
- Modify smart contracts or user balances
- Double-spend coins - They spend coins, wait for confirmation, then reverse that transaction by building a longer chain where the spending never happened. They get to keep the goods or services they bought and still have their original coins.
- Block transactions - They can refuse to include certain transactions in their blocks. This means users can’t send or receive funds until the attacker stops.
- Reorganize the blockchain - They can rewrite recent history. If you sent 10 BTC to someone yesterday, they can make that transaction disappear from the public ledger.
Real Attacks: It’s Happened Before
This isn’t theory anymore. In January 2019, Ethereum Classic (ETC) got hit twice in two days. Attackers double-spent over $1.1 million. Then in August 2020, they did it again-three more times. Total losses? Over $5 million. Bitcoin Gold suffered similar attacks in 2018. Monero, one of the most privacy-focused coins, got hit in August 2025. That shocked people because Monero had a strong hash rate and was thought to be safer. But attackers rented mining power from services like NiceHash and overwhelmed the network. Why these coins? Because they’re small. Bitcoin’s network has over 1.2 exahashes per second. To control half of that, you’d need billions of dollars in mining rigs and electricity costs. Impossible for most. But Ethereum Classic? Its hash rate is less than 5% of Bitcoin’s. A single mining farm with a few hundred rigs could take over.
Why Bigger Blockchains Are Safer
Bitcoin remains the most secure blockchain not because it’s perfect, but because it’s too expensive to attack. The cost to rent enough mining power for even a few hours is estimated at over $1 billion. And even if you pulled it off, the market would crash. Your stolen coins would be worthless because no exchange would touch them. The math is simple: attack cost > potential profit. For Bitcoin, that equation holds. For smaller chains? Not even close. A study from MIT’s Digital Currency Initiative found that many 51% attacks are profitable. Attackers don’t need to be rich-they just need to know where to rent cheap hash power. Services that rent out mining capacity make it easy. You pay $100,000 to rent for 24 hours. You double-spend $500,000. You walk away with $400,000 profit. That’s not a hack. That’s a business model.How to Spot a 51% Attack
Most networks don’t wait for disaster. They monitor for red flags:- Sudden chain reorganizations - when blocks get replaced after being confirmed
- Unusual spikes in orphaned blocks - blocks that get discarded because another chain became longer
- One mining pool suddenly controls over 40% of the hash rate

What’s Being Done to Stop It
There’s no silver bullet, but the industry is adapting:- More confirmations - Critical transactions now wait for 100+ blocks before being trusted.
- Hash rate monitoring - Networks alert users when mining power becomes too concentrated.
- Switching to Proof of Stake - Ethereum moved away from PoW. In PoS, you need to own 51% of the coins, not the hardware. That’s way harder and more expensive.
- Coordinated responses - Exchanges, miners, and developers now share threat intel. When an attack starts, they freeze funds and halt trading fast.
The Bigger Picture: Trust Is Fragile
Every time a 51% attack happens, the whole crypto market shudders. Prices drop. Investors flee. Exchanges delist the coin. It takes months to rebuild trust. The 2025 Monero attack was a wake-up call. If even a well-established, privacy-focused coin can be taken down, then no blockchain is truly safe. The lesson? Decentralization isn’t automatic. It’s fragile. It needs constant vigilance. The future of blockchain security isn’t just about better code. It’s about economics, coordination, and human behavior. The best defense isn’t a firewall. It’s a network of miners, exchanges, and users who refuse to let one group dominate.So, Should You Worry?
If you’re using Bitcoin or Ethereum? Probably not. The cost is too high. The risk is too low. But if you’re holding a lesser-known altcoin with a small hash rate? Pay attention. Check its mining distribution. Look at how many confirmations exchanges require. If it’s under 10, tread carefully. A 51% attack doesn’t mean the blockchain is broken. It means someone chose to abuse its rules. And if the cost of abuse is lower than the reward, someone always will.Can a 51% attack steal my cryptocurrency directly?
No. A 51% attack cannot access your private keys or withdraw funds from your wallet. The attacker can’t change who owns what. They can only reverse transactions that have already been confirmed, which means they can double-spend coins they themselves sent-not coins owned by others.
Why do smaller blockchains get attacked more often?
Smaller blockchains have lower total hash rates, meaning it takes far less mining power to control over 50%. For example, Bitcoin’s hash rate is over 1.2 exahashes per second, while Ethereum Classic’s is around 50 terahashes. That’s a 24,000x difference. Renting enough mining power to attack Ethereum Classic costs thousands, not billions.
Is Proof of Stake immune to 51% attacks?
No, but it’s much harder. In Proof of Stake, an attacker would need to own over 50% of all the coins in circulation. That’s expensive, and if they tried, the price would spike as people rushed to buy, making it unaffordable. Plus, if they succeeded, they’d destroy the value of their own holdings.
Can a 51% attack be stopped once it starts?
Yes, but it’s messy. Exchanges can freeze withdrawals. Miners can switch to a different chain. Developers can hard-fork the blockchain to invalidate the malicious blocks. These actions restore trust, but they also mean the network temporarily breaks its own rules-which defeats the purpose of decentralization. That’s why prevention is better than cure.
What happened during the Monero 51% attack in August 2025?
In August 2025, an unknown group rented enough mining power to control over 51% of Monero’s network. They double-spent over $10 million in transactions, targeting exchanges that accepted only 6 confirmations. The attack exposed a flaw in Monero’s mining algorithm, which made it easier to mine with ASICs than previously thought. The community responded with a hard fork to change the mining algorithm and prevent future attacks.

precious Ncube
February 26, 2026 AT 19:16Amita Pandey
February 27, 2026 AT 10:45Jan Czuchaj
March 1, 2026 AT 02:32Tracy Peterson
March 1, 2026 AT 15:23George Suggs
March 2, 2026 AT 21:15Dianna Bethea
March 4, 2026 AT 06:50KingDesigners &Co
March 4, 2026 AT 08:22Felicia Eriksson
March 5, 2026 AT 09:39aaron marp
March 5, 2026 AT 21:00Patrick Streeb
March 5, 2026 AT 22:12Phillip Marson
March 6, 2026 AT 01:20Tracy Whetsel
March 6, 2026 AT 01:23Alyssa Herndon
March 7, 2026 AT 02:34Ifeanyi Uche
March 7, 2026 AT 09:08Jeff French
March 7, 2026 AT 23:29Elana Vorspan
March 8, 2026 AT 00:08Kenneth Genodiala
March 8, 2026 AT 15:46Brian Lemke
March 9, 2026 AT 03:13Derek Sasser
March 10, 2026 AT 01:36